‘Smorgasbord’ would be an apt description for modern security systems. Because of the digitisation of their components, these systems are often a patchwork of technologies, protocols, and a variety of devices from multiple vendors.
The first challenge security systems integrators face is to get all these disparate devices on to a network, and then get that network configured and optimised.
But getting the environment set up and configured is just the first part of the struggle. The digitised nature of modern security systems introduces new points of failure in addition to the traditional ones.
For example, lost data has become a factor. With video data stored digitally, if something goes wrong – such as a storage device crashing or the network not transmitting data – video footage can be lost.
But perhaps the weakest point in modern security systems is the underlying network. Bottlenecks, bandwidth issues, or routing problems that prevent data being sent or received properly can all compromise a security system.
And if cyber criminals get access to the network or devices, they have the ability to negate the security of the entire system, to shut it down, or use devices for purposes other than those for which they were intended.
So how do you prevent these things from happening? The short answer is: you cannot completely circumvent these risks. Electronic devices will malfunction, networks will have bandwidth issues, and storage devices will fail.
These are the eternal truths of the digital world. All you can do is take preventative steps where possible, and set up alerts for when there is a failure. Enter network monitoring.
Monitoring the security system
As with other technologies, modern security systems have seen a convergence with traditional IT: you have the specialised security devices running on the same infrastructure as more operational IT devices such as switches, servers, routers and so on.
While this does add to the complexity of these systems, it also means there is the possibility to monitor everything in one place, despite the disparate technologies.
The same general steps that apply to monitoring traditional IT environments also apply to monitoring a security system network: establishing the metrics for a healthy system.
For example, how much bandwidth do specific devices use when operating normally? What does the traffic flow look like in different parts of the network at different times of day? What kind of CPU usage is normal for servers?
Based on the metrics from this monitoring you can set up thresholds and alerts. When values go above or below the "normal" values, then you know that you have a potential problem.
Using a good network monitoring solution it's possible to get a view of the entire network on one dashboard. Furthermore the information you get from monitoring the network can help you make adjustments to help prevent loss of data or critical failures.
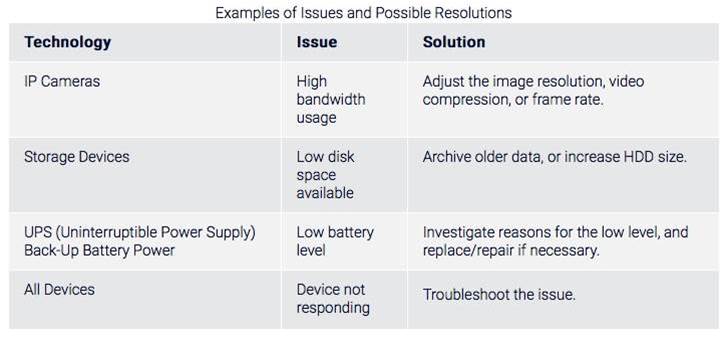
Take a look at some examples in the table below of potential issues you can pick up when monitoring a security system.
One of the advantages of network monitoring is its ability to monitor a wide variety of systems, as long as the connected devices offer standard technologies such as SNMP, NetFlow, WMI, etc.
While the monitoring approach remains the same - configure a sensor for a device and get statistics from that sensor - the actual network can look very different from one installation to another.
So with the same network monitoring principle, you might be monitoring a hospital, a smart home, a smart city...or a physical security system.